Workday Security Management
Introduction
When you hear discussions about Workday Security, the reasoning is generally to determine whether someone can see or edit particular data items in your Workday tenant, or if they can perform particular activities during an event. Workday Security is based on the following principles and assumptions:
- Settings are intended to be preventative and automated wherever possible.
- The settings are risk-based, with control efforts made when risks associated with processes merit the implementation of these levels of control. The cost of these controls should not outweigh risk. In other words, the system security should not be built in such a manner that it prevents users from properly utilizing the features available in Workday.
- All of these settings should always be documented, and clearly communicated to impacted users and administrators. They should also be monitored to ensure that they remain effective.
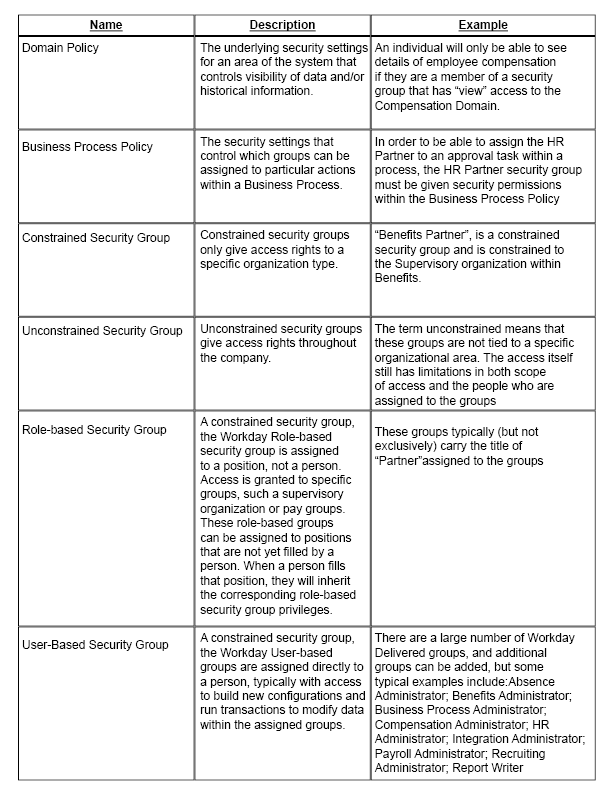
Workday Security is controlled through a range of security groups. These groups are then assigned to the Domain security settings or the Business Process Policies in order to allow the members of those groups to have the visibility, or access pertaining to those areas.
Security groups can consist of a large number of users, or a very small number of users. In some cases this may mean just one or two people. There are overall groups that allow broad visibility, “Employee As Self” being one of these. Changes to the settings for that group will impact the entire employee population.
Additionally, certain data elements are considered to be very sensitive, any Social Security Numbers for example. As such the domain settings for those data elements (Workday Business Objects) are restricted to only be visible by specific security groups.
The vast majority of Workday users do not have any data access beyond that which is granted to Employees through the “Employee As Self” security group. This is the baseline setting within the system, and while there are default settings set up to all Workday clients during their initial implementation, each tenant may have slightly different settings for this core group.
The next most populated level of security is the “Manager As Self” group. This is overlaid on the “Employee As Self” group, with additional access to allow managers the visibility to sensitive data for their subordinates, and the ability to perform applicable tasks for their role as a manager.
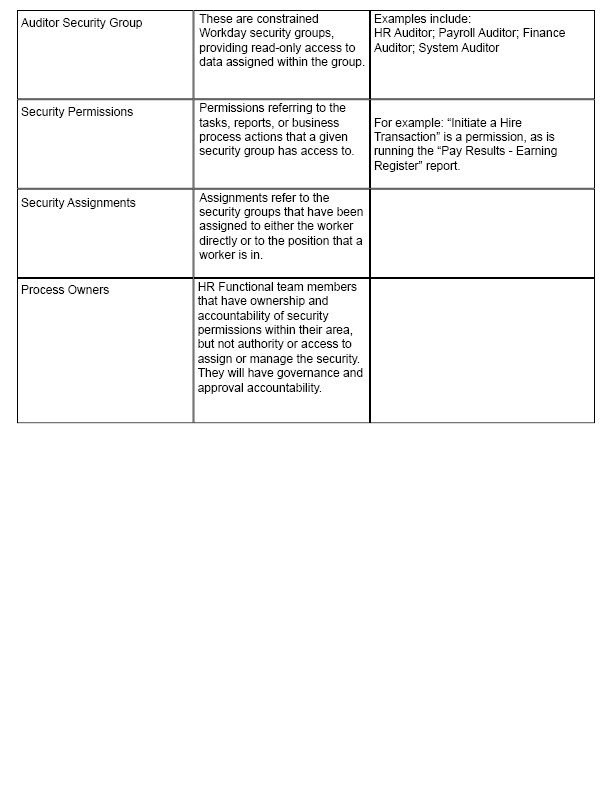
1: Workday Security Terminology
As previously mentioned, Workday Security is assigned to the various security groups. The most commonly used (and edited) are role-based security groups, and user based security groups. Those details are listed below.
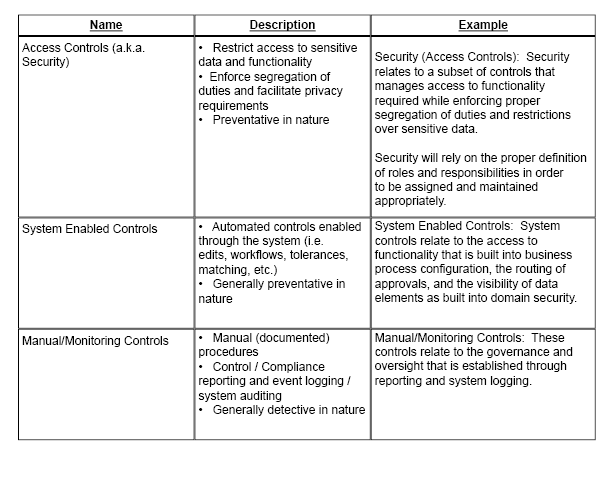
2: System Security Controls
When considering data security, it is important to remember that Workday Security settings are only a piece of the puzzle. Overall System Security Controls are much broader, and include activities and techniques that address regulatory, financial and operating risks associated with processes.
Some Controls are preventative, to avoid problems from occurring in the first place. Others are detective in nature, intended to discover issues that occur. They are broadly categorized into the following types:
3: Authentication Policy (Location Limitation rules)
In addition to the security settings, it is sometimes deemed necessary to carefully control where people can physically have the ability to perform administrative changes to Workday. This is particularly important when an organization wants to restrict the performance of admin activity to only take place within the company network. In order to do this, the following restrictions can be built into Workday’s “Authentication Policy” configuration.
- Workday can be setup so that it is accessed from any internet location (IP Address) for accessing an individual’s personal information as self-service actions
- Administrator Access for any advanced security group (Role Based or User Based) can be limited so that it can only be accessed from within the company Network
- People with Implementer accounts typically have full system access from any internet location (IP Address)
- Company Networks are assigned specifically by IP Address
- As new IP Addresses are added by the company’s IT department, they are added to the Authentication Policy.
In this day in age, security is at the forefront of everyone’s mind. This breakdown of possibilities within Workday, and everyone having the appropriate permissions, gives you peace of mind that your company is secure.
If you want to learn more, check out our insights or reach out to us at info@syssero.com
